How We Think About Security at Miru
Encryption, authentication, role-based access, open source auditing, and self-hosting. How Miru protects your billing data.

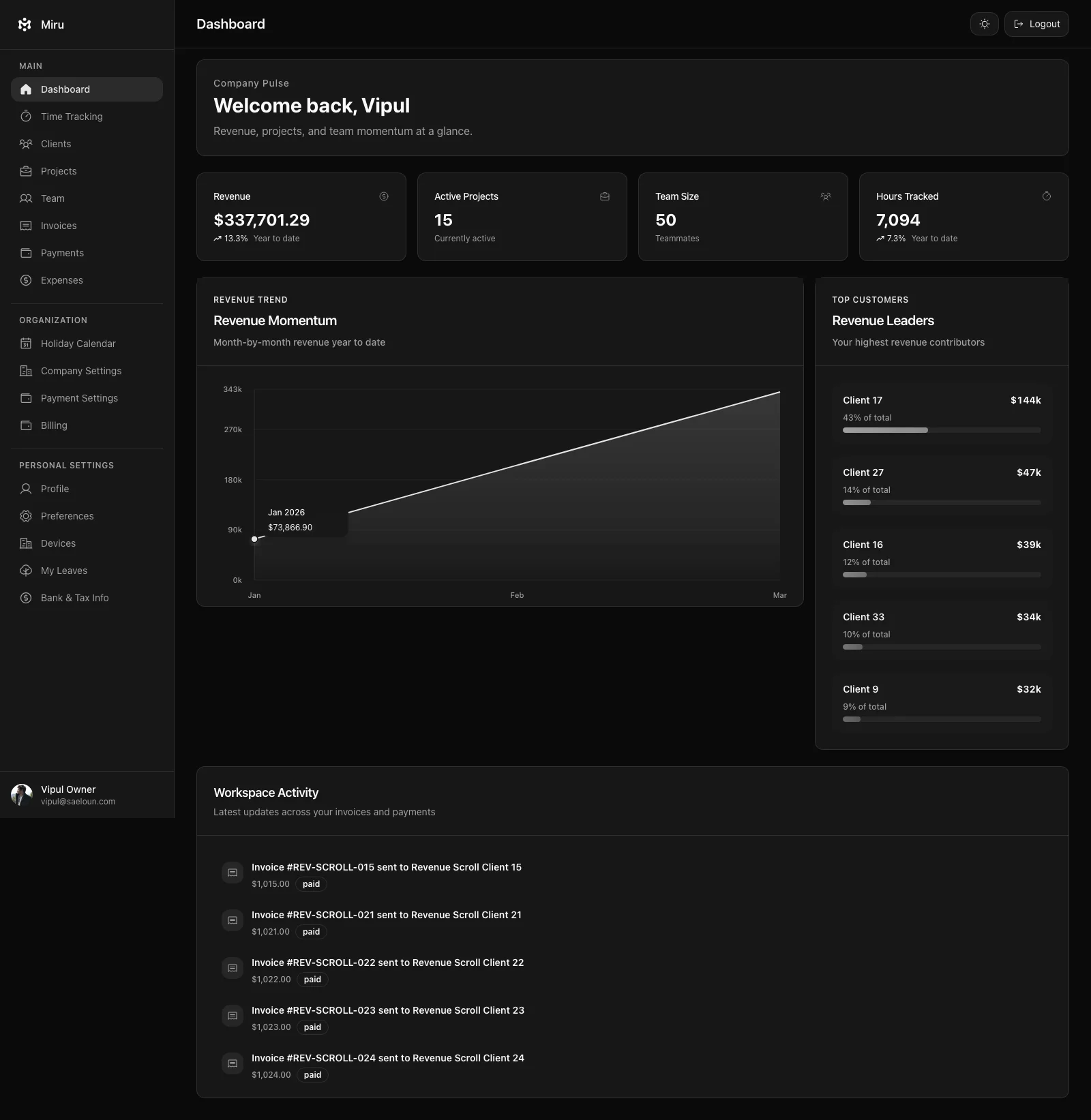
People trust Miru with their billing data. Client names, project rates, invoice amounts, payment records. That’s sensitive information. We don’t take that lightly.
Here’s how we actually think about security. Not the marketing version. The engineering version.
Encryption Is Table Stakes
All data in transit uses TLS 1.3. All data at rest is encrypted with AES-256. Database backups are encrypted. This isn’t a feature we’re proud of. It’s the minimum. Any product handling financial data that doesn’t do this in 2026 isn’t paying attention.
PostgreSQL with automated daily backups and point-in-time recovery. We can restore to any point in the last 30 days. Backups are stored in a separate geographic region from the primary database. If the data center catches fire, your data survives.
Authentication That Doesn’t Annoy People
Session-based authentication with secure token rotation. We deliberately chose sessions over JWTs for the web app because sessions can be invalidated server-side immediately. If an account is compromised, we revoke the session and it’s done. No waiting for a JWT to expire.
OAuth via Google for teams that already use Google Workspace. One less password to manage.
The CLI uses dedicated bearer tokens. You generate a token from the automation settings page, scope it to your account. It’s separate from your session. You can revoke it without logging out of the web app. If a CI/CD script gets compromised, you revoke that one token and nothing else is affected.
Five Roles, Least Privilege
Admin, Owner, Book Keeper, Employee, Client. That’s it.
Every role sees only what it needs. Employees track time and submit expenses. They can’t see client billing rates. Book keepers manage invoices and payments. They can’t modify team settings or delete projects. Clients see their own invoices and nothing else.
We didn’t build a 47-row permission matrix with checkboxes. We sat down and asked: for each role, what’s the minimum set of things they need to do? That’s what they can access. Everything else is hidden, not just disabled.
Open Source Is a Security Feature
Most security pages say “we take security seriously” and leave it at that. You’re supposed to trust them. With Miru, you don’t have to trust us. You can verify.
Every line of code is on GitHub. The authentication logic. The authorization checks. The database queries. The API endpoints. All of it. If there’s a vulnerability, anyone can find it, report it, and submit a fix.
This isn’t security through obscurity. It’s the opposite. We’re betting that transparency makes us more secure, not less. The open-source community has found and fixed bugs in Miru that our internal team missed. That’s the model working as intended.
Self-Host for Maximum Control
If your compliance requirements say “no third-party data processors,” self-host Miru. Your servers, your database, your network. Nothing leaves your environment.
Deploy with Docker in minutes. Full setup guides for macOS, Ubuntu, Windows, and Docker Compose in the docs. You get the same product. You control the infrastructure.
For regulated industries — healthcare, finance, government contracting — self-hosting eliminates an entire category of compliance risk. No vendor security questionnaires. No data processing addendums. Your data never touches our servers.
Responsible Disclosure
Found something? Email security@saeloun.com. We respond within 24 hours. We investigate immediately. We credit researchers in our security advisories.
We don’t have a bug bounty program yet. We’re a small team and we’d rather put that budget into engineering. But we take every report seriously and fix vulnerabilities fast.
SOC 2 Type II is in progress. GDPR compliant. Data processing addendum available on request.
Read the full details on our security page.
Vipul A M
Co-founder at Saeloun. Building Miru. Rails contributor. Shipping from Pune, India.
Read next
Miru Now Supports 2FA: Authenticator Apps and Passkeys
Your Miru account just got a lot more secure. TOTP authenticator apps and passkey sign-in are live today.
How We Track Time with AI Agents and the Miru CLI
A practical guide to automated time tracking for teams using Claude Code, Codex, and other AI coding tools. Real workflows, real scripts, zero browser tabs.
Dark Mode Done Right: Why Most Apps Get It Wrong
CSS invert() is not dark mode. Here's what it actually takes to build a dark theme that doesn't hurt your eyes.
The article is the theory. Miru is the workflow.
If this post is about better billing, cleaner tracking, or fewer tools, Miru is the product version of that argument.
